Product
Solutions
Teams
Customers
Resources
Guides
Latest Blog
May 20, 2026

Why we got rid of our small-PR rule
Pricing


Designed with RBAC depth, private incident controls, and flexibility to run every investigation without compromise.








Certified across the compliance standards security teams require—and paired with IaC-native provisioning—governance-as-code isn’t an aspiration; it’s how Rootly operates.

Granular RBAC across incident roles, services, teams, and components. Control exactly who sees what—across every stage of a sensitive investigation.
Private incidents are invisible to the rest of the org by default. Access is invite-only, access-controlled end-to-end, and never something somebody accidentally stumbles into.
Everything is logged as it happens. When regulators ask what occurred, the answer is already documented—not reassembled from Slack threads and memory.
100+ integrations—SIEMs, SORARs, identity providers, on-prem systems—so your response process doesn't depend on swapping tools out.
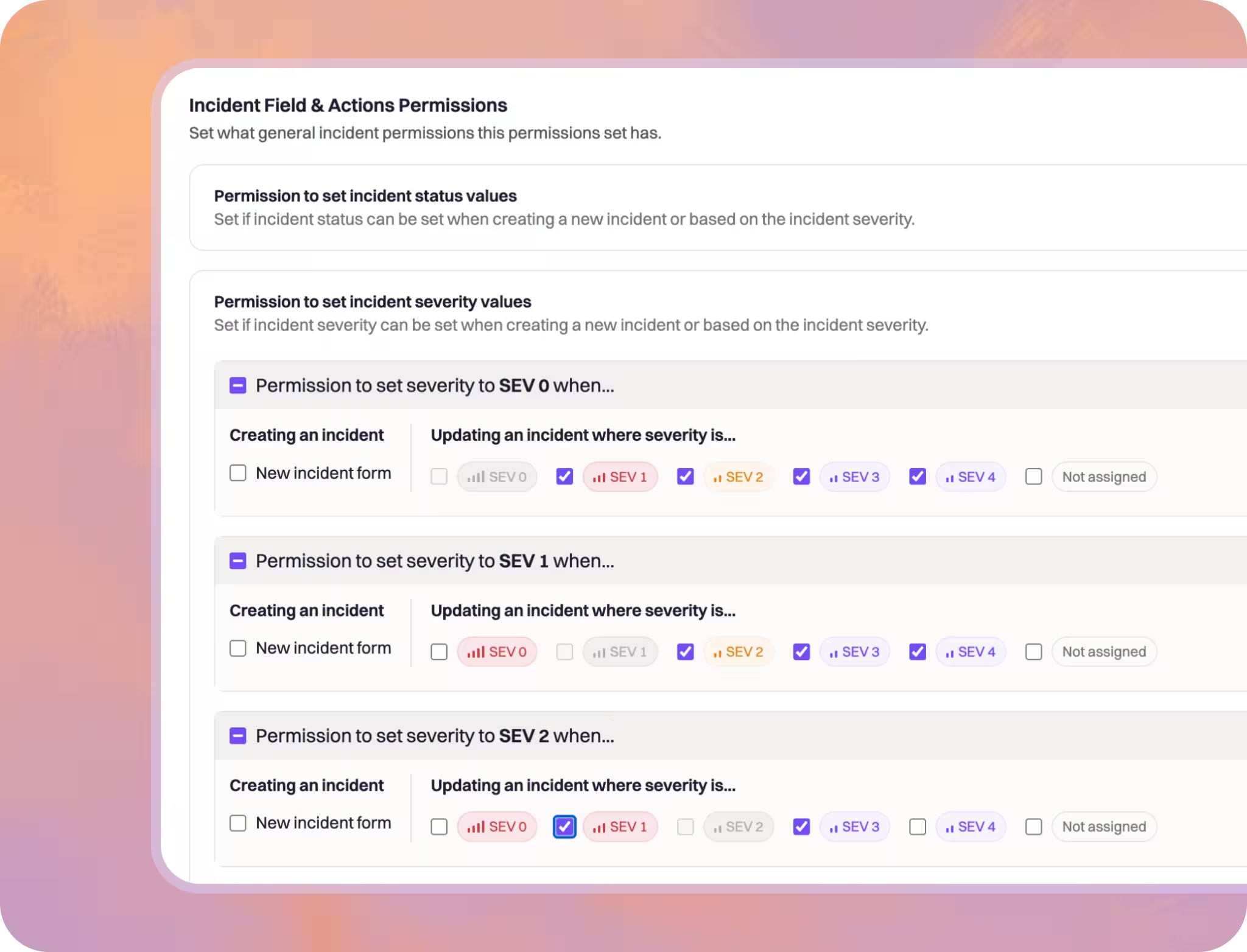
Control exactly who sees and performs what actions across every stage of a sensitive investigation—by role, team, service, component, severity, and incident type.
Grant just-in-time access when an incident fires, revoke it automatically when it closes, and extend those permissions to connected docs without a single manual step.
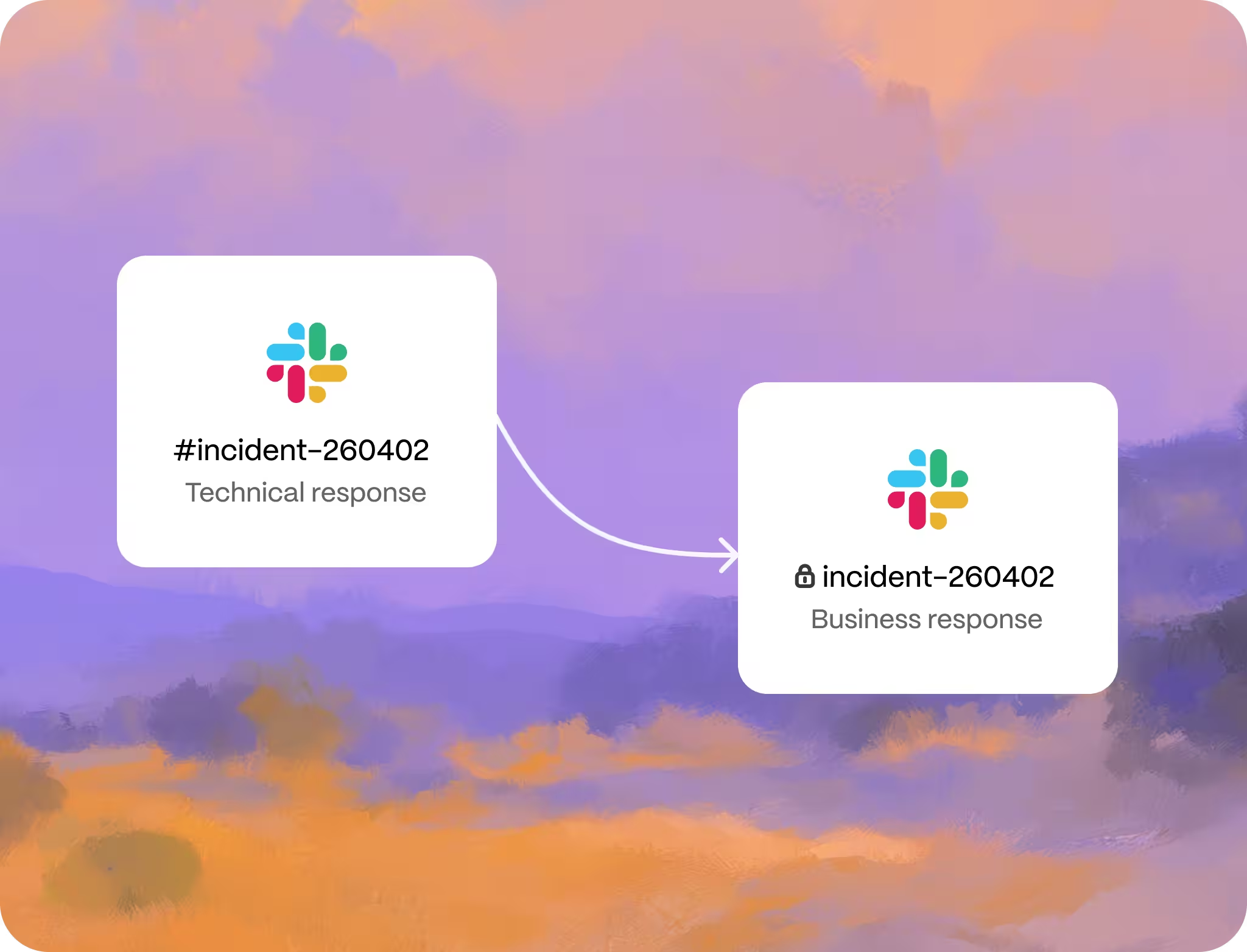
Run security incidents across two parallel Slack channels—one for technical response, one for legal and business—where incident updates flow one way but sensitive discussions never cross over.
If your InfoSec team needs full separation, Rootly supports isolated tenants so operations are entirely independent from the rest of the organization.
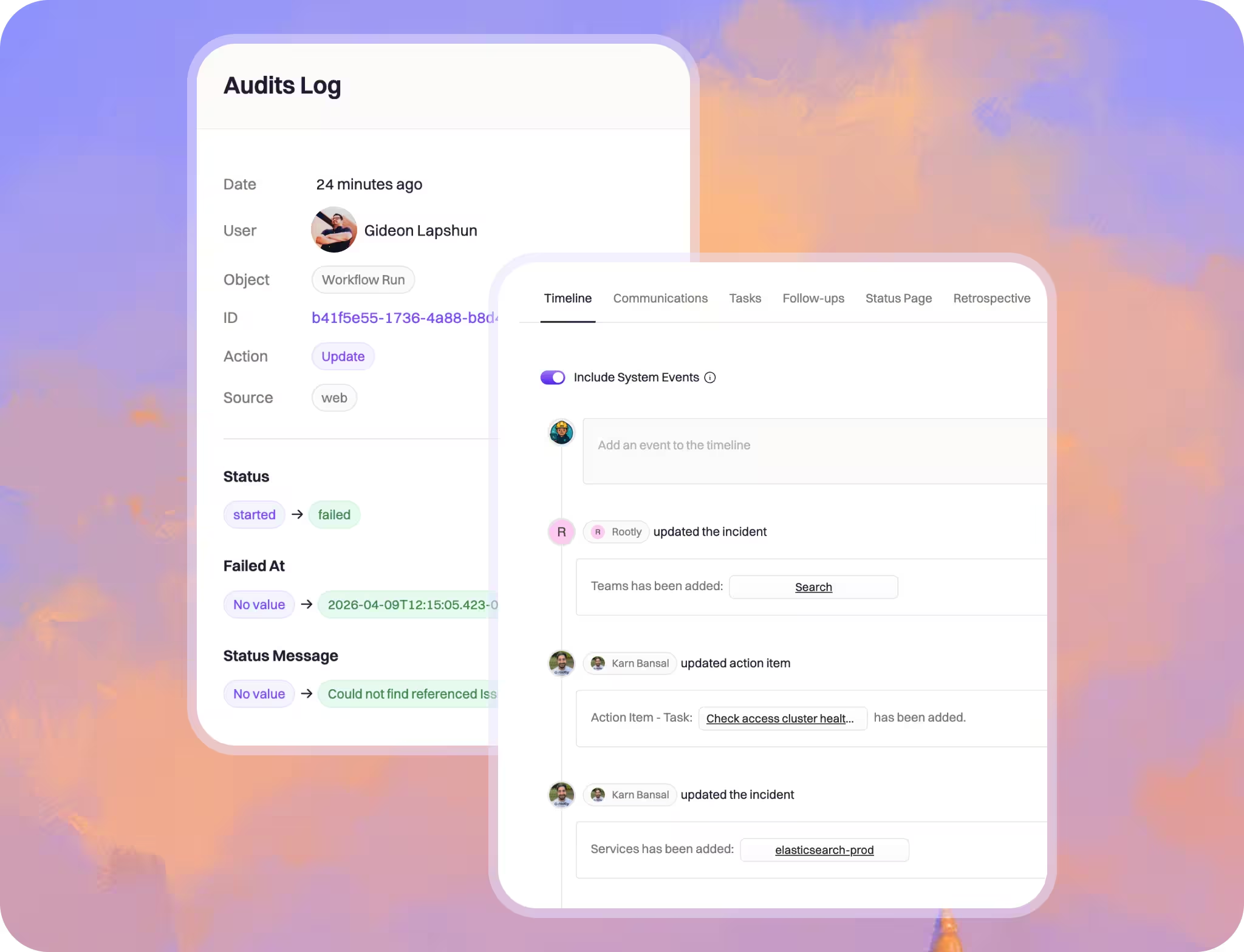
Every action, decision, and escalation is logged to a single incident record in real time—no reconstruction required when regulators come calling. Access logs included: who was granted entry, when, and when it was revoked.